Cloud Security Platforms Explained: How to Secure Digital Infrastructure at Scale
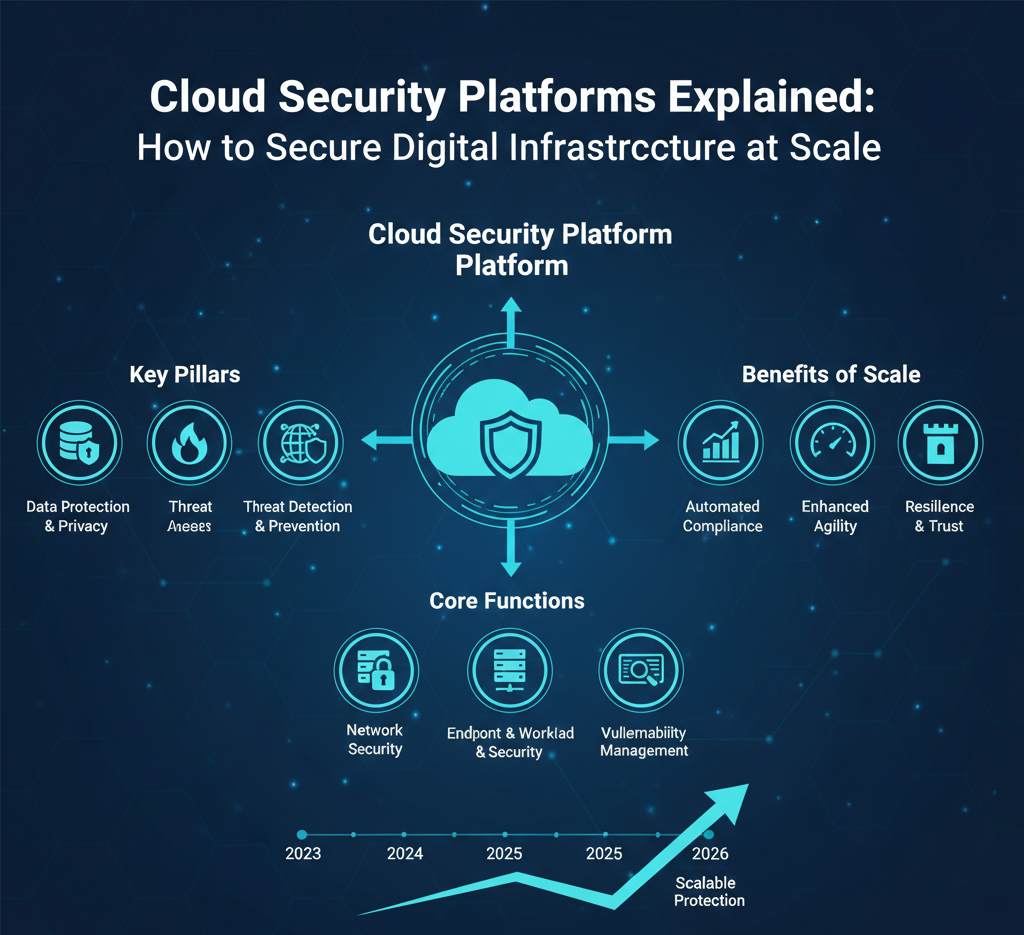
As enterprises accelerate cloud adoption, security has become one of the most critical — and complex — challenges in modern IT. In 2026, organizations are no longer protecting a single data center. Instead, they are securing distributed cloud environments that span multiple providers, regions, applications, and remote users.
Cloud security platforms are designed to solve this problem at scale. They provide visibility, protection, and control across dynamic digital infrastructure while helping businesses stay compliant, resilient, and agile.
This article explains what cloud security platforms are, how they work, and how organizations can use them to protect digital infrastructure without slowing innovation.
Why Cloud Security Is Different From Traditional Security
Traditional security models were built around static environments: fixed networks, known devices, and predictable access patterns. Cloud infrastructure changes that entirely.
Modern cloud environments are:
-
Highly dynamic and elastic
-
Shared across multiple cloud providers
-
Accessed by remote teams and third-party tools
-
Powered by APIs, containers, and microservices
Because of this, perimeter-based security alone is no longer enough. Cloud security platforms focus on continuous monitoring, identity-based access, and real-time threat prevention, rather than fixed network boundaries.
What Is a Cloud Security Platform?
A cloud security platform is a centralized solution that protects cloud-based infrastructure, workloads, applications, and data. It integrates security controls directly into cloud environments and provides unified visibility across services such as:
-
Public cloud (AWS, Azure, Google Cloud)
-
Hybrid and multi-cloud architectures
-
Containers and Kubernetes
-
Serverless applications
-
SaaS platforms and APIs
Rather than relying on manual configurations, these platforms use automation and intelligence to adapt to changes in real time.
Core Components of Cloud Security Platforms

Most modern cloud security platforms combine several key capabilities into a single framework.
1. Identity and Access Management (IAM)
Identity is now the new security perimeter. Cloud security platforms enforce strict access controls based on who the user is, what device they are using, and what they are allowed to do.
Key features include:
-
Role-based and least-privilege access
-
Multi-factor authentication
-
Continuous identity verification
-
Secure access for remote and hybrid teams
By controlling access at the identity level, organizations significantly reduce the risk of breaches caused by compromised credentials.
2. Cloud Workload Protection
Cloud workloads include virtual machines, containers, and serverless functions. These assets are often short-lived, making manual security nearly impossible.
Cloud security platforms protect workloads by:
-
Monitoring runtime behavior
-
Detecting malware and suspicious activity
-
Blocking unauthorized processes
-
Securing containers and orchestration environments
This ensures that even fast-moving infrastructure remains protected.
3. Cloud Security Posture Management (CSPM)
Misconfigurations are one of the leading causes of cloud breaches. CSPM tools continuously scan cloud environments for risky settings, exposed resources, and compliance gaps.
Benefits of CSPM include:
-
Automated configuration checks
-
Continuous compliance monitoring
-
Risk prioritization and remediation guidance
-
Visibility across multiple cloud accounts
CSPM helps teams fix issues before attackers can exploit them.
4. Data Protection and Encryption
Data in the cloud moves constantly — between services, users, and regions. Cloud security platforms protect sensitive information through:
-
Encryption at rest and in transit
-
Data loss prevention policies
-
Secure key management
-
Monitoring of data access patterns
These controls help organizations meet regulatory requirements while maintaining performance and scalability.
5. Threat Detection and Response
Modern cloud security platforms use AI and behavioral analytics to detect threats that traditional tools often miss.
They can:
-
Identify abnormal user or workload behavior
-
Detect lateral movement inside cloud environments
-
Trigger automated incident response actions
-
Reduce response time from hours to seconds
This proactive approach is essential for defending large-scale digital infrastructure.
Securing Cloud Infrastructure at Scale

Scaling security requires more than adding tools — it requires the right strategy.
Centralized Visibility
Security teams need a single view of assets, identities, risks, and threats across all cloud environments. Centralized dashboards reduce blind spots and simplify decision-making.
Automation by Default
Manual security processes don’t scale. Automated policy enforcement, remediation, and response allow organizations to maintain security even as infrastructure grows.
Zero Trust Architecture
Zero Trust assumes no user or workload is trusted by default. Every request is verified, reducing the impact of compromised accounts or systems.
Integration With DevOps
Security works best when embedded into development pipelines. Cloud security platforms integrate with CI/CD workflows to detect risks early, without slowing deployment.
Business Benefits of Cloud Security Platforms
Beyond protection, cloud security platforms deliver clear business value:
-
Reduced breach risk and downtime
-
Faster cloud adoption with fewer security roadblocks
-
Improved compliance and audit readiness
-
Lower operational costs through automation
-
Stronger customer and partner trust
When security is built into infrastructure, organizations can innovate confidently.
Final Thoughts

In 2026, cloud security is no longer optional or secondary — it is foundational. As digital infrastructure becomes more complex and distributed, cloud security platforms provide the visibility, automation, and intelligence needed to protect systems at scale.
Organizations that invest in the right cloud security strategy don’t just reduce risk. They create a secure foundation for growth, agility, and long-term digital success.